Making Remote Research Work
March 23, 2022
Working with a group can always have challenges, especially so when the group members are not in the same location.
Six Dakota State University graduate students – all in different physical locations -- are learning to work through those challenges, and are successfully collaborating on a research project.
The students – and their faculty advisor Dr. Cody Welu – are spread out over the U.S. and Great Britain, so “finding times to meet with a geographically diverse group can be difficult,” Welu stated, but “the students are all great and seemed to work together very well.” Welu is an Assistant Professor at The Beacom College of Computer and Cyber Sciences.
This project did require planning and communication, said Jacob Williams a doctoral student in Cyber Operations. He is originally from Parker, SD, now living in Columbia, MD.
“Working professionally across almost every possible time zone in the continental U.S. required a lot of planning. Schedules were often tight and not everyone was able to make it to each meeting. Proper note-taking and asynchronous communication have been a must. The ability to work independently was instrumental in keeping progress moving,” Williams said.
To begin, “we did an initial intro of ourselves and our strengths, then split the work based on tasks that highlighted our strengths or learning,” said Chinyere “Chin” Isaac-Heslop, a Cyber Operations Ph.D. student from London, England.
Roles “were largely chosen based on a growth perspective and what interested each person individually,” Williams added. “Being able to utilize each person’s professional experience and play to their strengths was super useful,” he added.
“Whenever a diverse group is brought together, there is much to be learned and much to be gained by all,” Welu said. “The different skillsets the team brings to the table are vital for project success.”
He added that “while all the student researchers are studying cyber-security in some way, they all bring a different background and different experiences to the table.”
Even remotely, the opportunity to conduct research can give graduate students essential hands-on experience with various research methods, Welu said, but “I think what makes this research unique is it is immediately applicable in the real world. Our students had the opportunity to conduct needed research for a government agency, research that will have immediate applicability.”
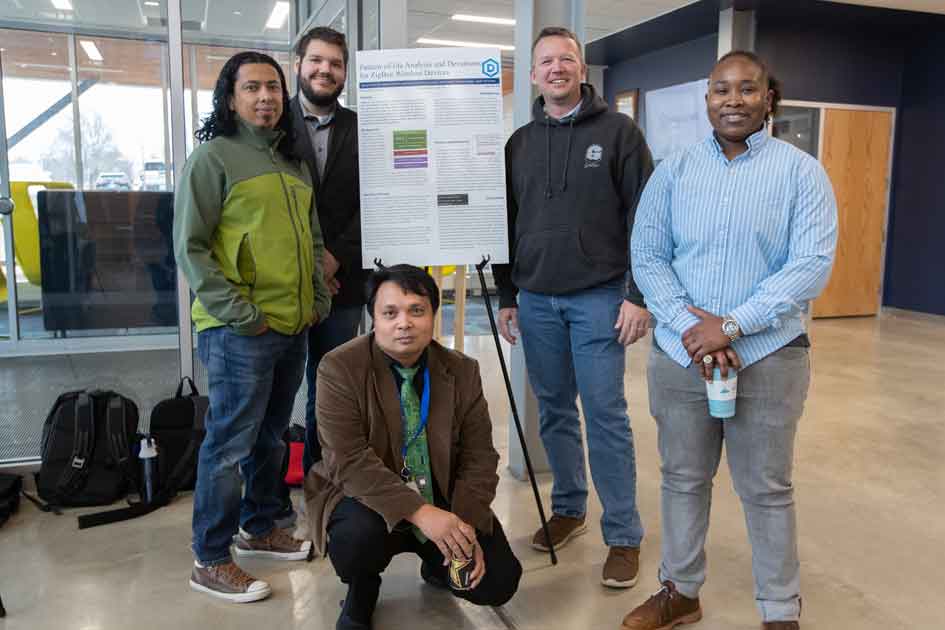
The project, titled “Pattern-of-life Analysis and Deviations for ZigBee Wireless Devices,” was one of the Graduate Research Initiative grants awarded to students this academic year. It includes a $500 stipend which may be used for collection, analysis, or results dissemination. In addition to Isaac-Heslop and Williams, the other student researchers are Briant Becote, Mar Castro, Kurt Jarvis, Subash Adhikari, and Joseph Padron.
“This research looks at various devices communicating over a specific wireless protocol (ZigBee) in an effort to identify specific devices and possibly security issues through ZigBee network traffic,” Welu said.
Success on this project could include, at a high level, being able to identify traffic originating from IOT devices, particularly the ability to identify a compromise, which is a significant step to improving the security of these devices and the networks to which they are connected, he stated.
“The privacy and security of IOT devices are rarely a priority when designing the product, making it even more important for security researchers to evaluate such devices,” Welu continued.
Williams appreciated this opportunity.
“I’m very grateful that Dakota State University places such a high importance on student research and provides the necessary support to be able to carry it out.”